Review the exhibit.
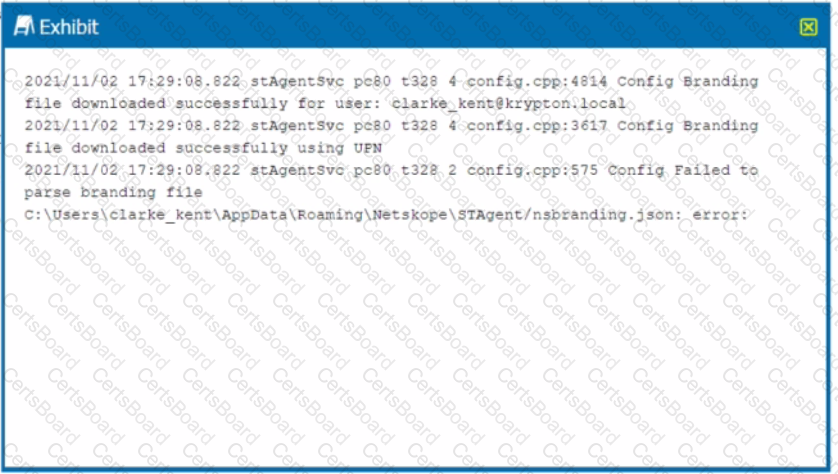
You receive a service request from a user who indicates that their Netskope client is in a disabled state. The exhibit shows an excerpt (rom the affected client nsdebuglog.log.
What is the problem in this scenario?
You are an administrator writing Netskope Real-time Protection policies and must determine proper policy ordering.
Which two statements are true in this scenario? (Choose two.)
Your company has a Symantec BlueCoat proxy on-premises and you want to deploy Netskope using proxy chaining. Which two prerequisites need to be enabled first in this scenario? (Choose two.)
You want to prevent a document stored in Google Drive from being shared externally with a public link.
You are using the Netskope DLP solution. You notice flies containing test data for credit cards are not triggering DLP events when uploaded to Dropbox. There are corresponding page events. Which two scenarios would cause this behavior? (Choose two.)
Your team is asked to investigate ten Netskope DLP incidents. You want to assign these incidents among different team members.
You are integrating Netskope tenant administration with an external identity provider. You need to implement role-based access control. Which two statements are true about this scenario? (Choose two.)
Review the exhibit.
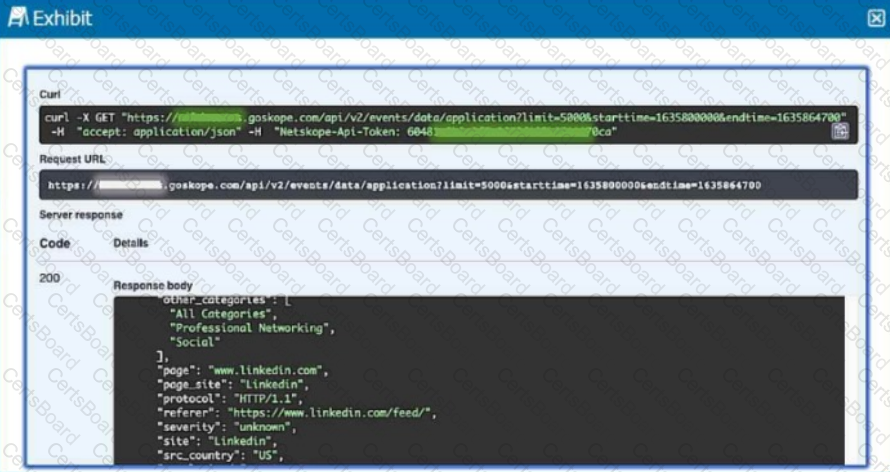
Referring to the exhibit, which three statements are correct? (Choose three.)
Review the exhibit.
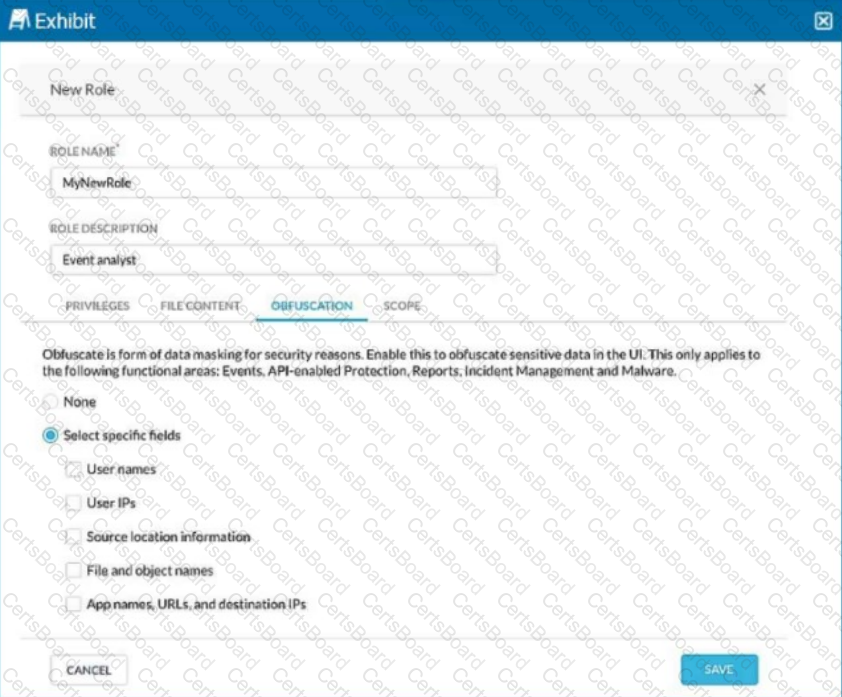
You are asked to create a new role that allows analysts to view Events and Reports while providing user privacy. You need to avoid directly exposing identities and user location information.
Which three fields must you obfuscate in this scenario? (Choose three.)
Review the exhibit.
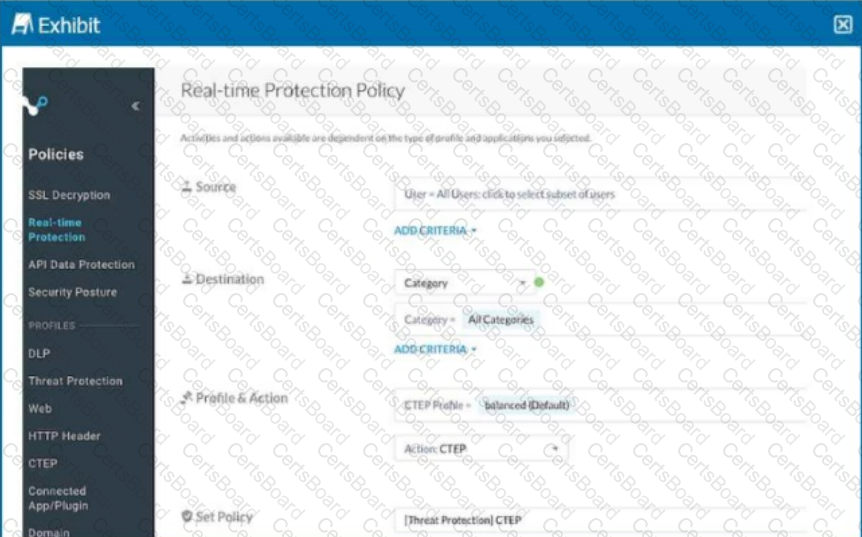
Your Real-time Protection policy contains some rules with only a browse activity. The exhibit shows a new policy rule.
Where is the correct location to place this rule?


