
Last Update Apr 21, 2025
Total Questions : 60 With Comprehensive Analysis

Last Update Apr 21, 2025
Total Questions : 60


PECB Certified ISO/IEC 27005 Risk Manager
Last Update Apr 21, 2025
Total Questions : 60 With Comprehensive Analysis
Why Choose CertsBoard
Customers Passed
PECB ISO-IEC-27005-Risk-Manager
Average Score In Real
Exam At Testing Centre
Questions came word by
word from this dump

Try a free demo of our PECB ISO-IEC-27005-Risk-Manager PDF and practice exam software before the purchase to get a closer look at practice questions and answers.

We provide up to 3 months of free after-purchase updates so that you get PECB ISO-IEC-27005-Risk-Manager practice questions of today and not yesterday.

We have a long list of satisfied customers from multiple countries. Our PECB ISO-IEC-27005-Risk-Manager practice questions will certainly assist you to get passing marks on the first attempt.

CertsBoard offers PECB ISO-IEC-27005-Risk-Manager PDF questions, web-based and desktop practice tests that are consistently updated.

CertsBoard has a support team to answer your queries 24/7. Contact us if you face login issues, payment and download issues. We will entertain you as soon as possible.

Thousands of customers passed the PECB Designing PECB Azure Infrastructure Solutions exam by using our product. We ensure that upon using our exam products, you are satisfied.
Scenario 1
The risk assessment process was led by Henry, Bontton’s risk manager. The first step that Henry took was identifying the company’s assets. Afterward, Henry created various potential incident scenarios. One of the main concerns regarding the use of the application was the possibility of being targeted by cyber attackers, as a great number of organizations were experiencing cyberattacks during that time. After analyzing the identified risks, Henry evaluated them and concluded that new controls must be implemented if the company wants to use the application. Among others, he stated that training should be provided to personnel regarding the use of the application and that awareness sessions should be conducted regarding the importance of protecting customers’ personal data.
Lastly, Henry communicated the risk assessment results to the top management. They decided that the application will be used only after treating the identified risks.
Based on scenario 1, Bontton used ISO/IEC 27005 to ensure effective implementation of all ISO/IEC 27001 requirements. Is this appropriate?
According to ISO/IEC 27000, what is the definition of information security?
Scenario 8: Biotide is a pharmaceutical company that produces medication for treating different kinds of diseases. The company was founded in 1997, and since then it has contributed in solving some of the most challenging healthcare issues.
As a pharmaceutical company, Biotide operates in an environment associated with complex risks. As such, the company focuses on risk management strategies that ensure the effective management of risks to develop high-quality medication. With the large amount of sensitive information generated from the company, managing information security risks is certainly an important part of the overall risk management process. Biotide utilizes a publicly available methodology for conducting risk assessment related to information assets. This methodology helps Biotide to perform risk assessment by taking into account its objectives and mission. Following this method, the risk management process is organized into four activity areas, each of them involving a set of activities, as provided below.
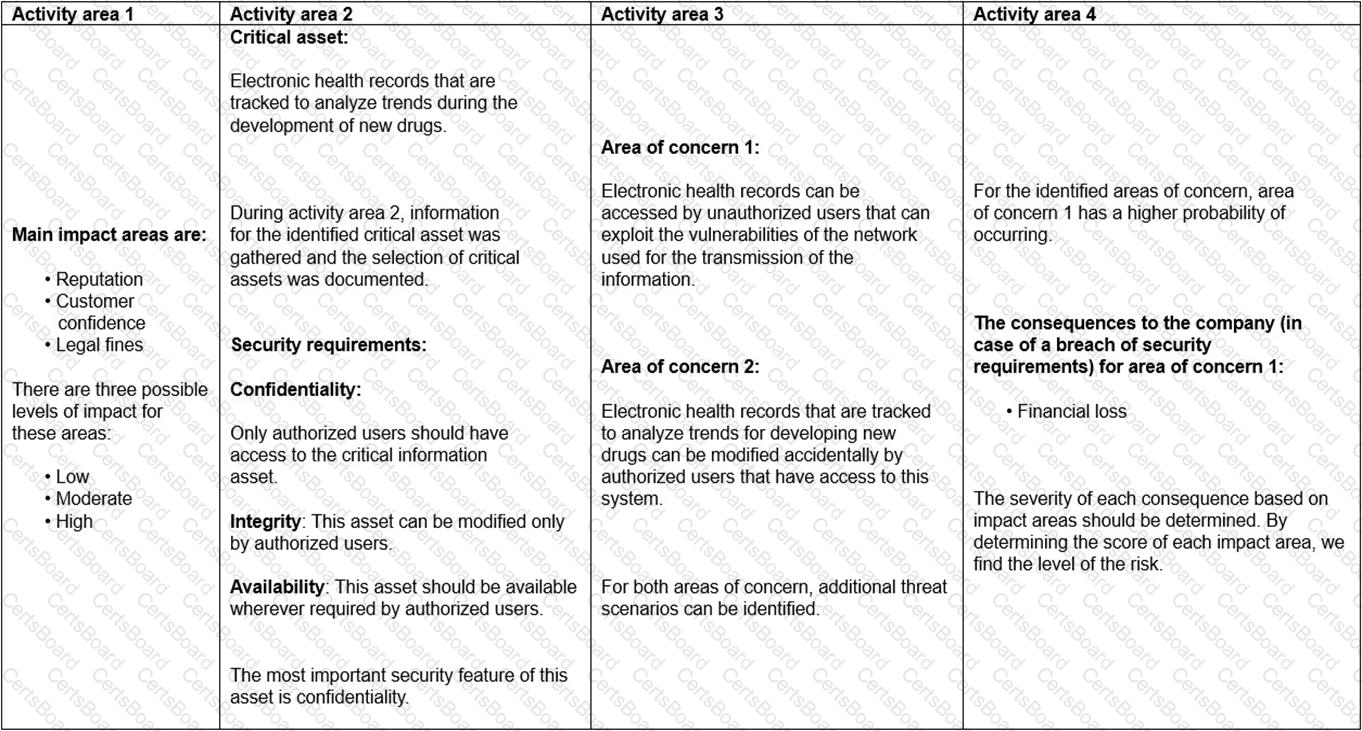
1. Activity area 1: The organization determines the criteria against which the effects of a risk occurring can be evaluated. In addition, the impacts of risks are also defined.
2. Activity area 2: The purpose of the second activity area is to create information asset profiles. The organization identifies critical information assets, their owners, as well as the security requirements for those assets. After determining the security requirements, the organization prioritizes them. In addition, the organization identifies the systems that store, transmit, or process information.
3. Activity area 3: The organization identifies the areas of concern which initiates the risk identification process. In addition, the organization analyzes and determines the probability of the occurrence of possible threat scenarios.
4. Activity area 4: The organization identifies and evaluates the risks. In addition, the criteria specified in activity area 1 is reviewed and the consequences of the areas of concerns are evaluated. Lastly, the level of identified risks is determined.
The table below provides an example of how Biotide assesses the risks related to its information assets following this methodology:
Based on scenario 8, how should Biotide use the criteria defined in the activity area 1?